Since I took CCNA I have always tried to renew my certifications with exams from other tracks.
Now with Cisco U and the Rev Up program it becomes even easier to get CE credits and at the same time delve into other technologies.

Since I took CCNA I have always tried to renew my certifications with exams from other tracks.
Now with Cisco U and the Rev Up program it becomes even easier to get CE credits and at the same time delve into other technologies.

A customer called because they expect the Internet access in the DC to reach 10 Gbps, but a speedtest only shows 1 Gbps throughput.
Once again, it’s a network issue. Or not?
In my role as a network architect, I often find myself validating a design based on documentation provided by the vendor. Whenever possible, I prefer to verify at least the core functionality in the lab.
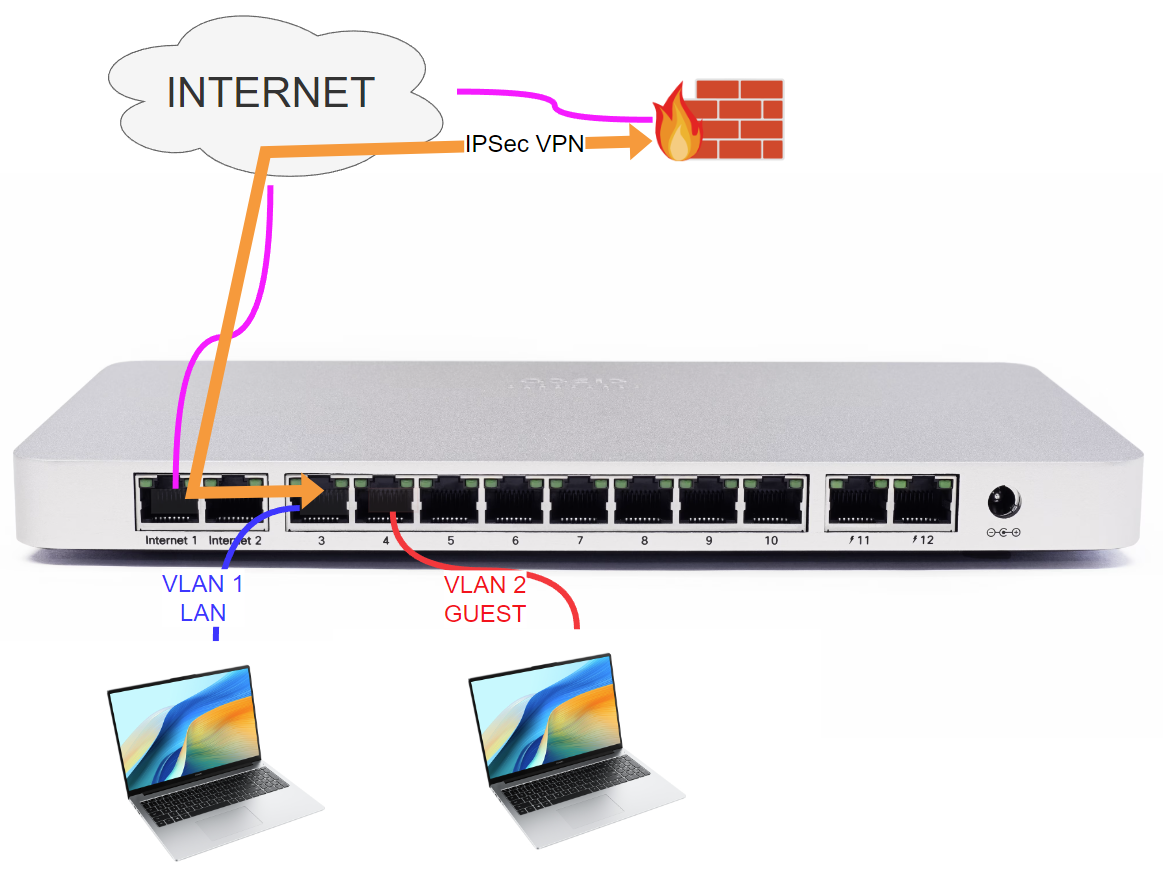
Platforms such as Cisco Meraki on the one hand simplify configurations by introducing automation and abstraction mechanisms that have a great impact on large installations; on the other hand, abstractions and simplifications require careful analysis of requirements and deployment methods.
In this blog I present a scenario that I had the opportunity to test recently.

When chatting with both colleagues and customers about BGP path manipulations, I’ve picked up on something interesting – the concept of admin distance can often lead to some head-scratching moments.
So, in this blog post, I’m going to take you through a few links and hands-on labs. Our goal? To unravel the mysteries surrounding admin distance and its pivotal role in the BGP best path selection process. Let’s dive in!
I was recently engaged in a troubleshooting session pertaining to Azure Network Load Balancers (NLBs).
The assistance was sought by cloud engineers seeking deeper insights into the operational characteristics of NLBs. The findings are outlined below.
On the second day of Network Field Day 31 BackBox presented their automation tool.
On April 25th 2023 Google Cloud has an incident involving a datacenter. The incident impacted multiple zones.
If this sounds strange, it is because not all cloud zones are created equal.
I’m happy to be part again of the Tech Field Day delegates attending Networking Field Day 31 on April 12-13, 2023.

Ten years ago I passed the CCIE RS lab exam , now renamed CCIE Enterprise Infrastructure .
